Remote work has become a reality for organizations across most industries. What started as a pandemic survival strategy has evolved into a mainstay. In fact, 72% of companies are planning on permanently allowing some level of remote work.
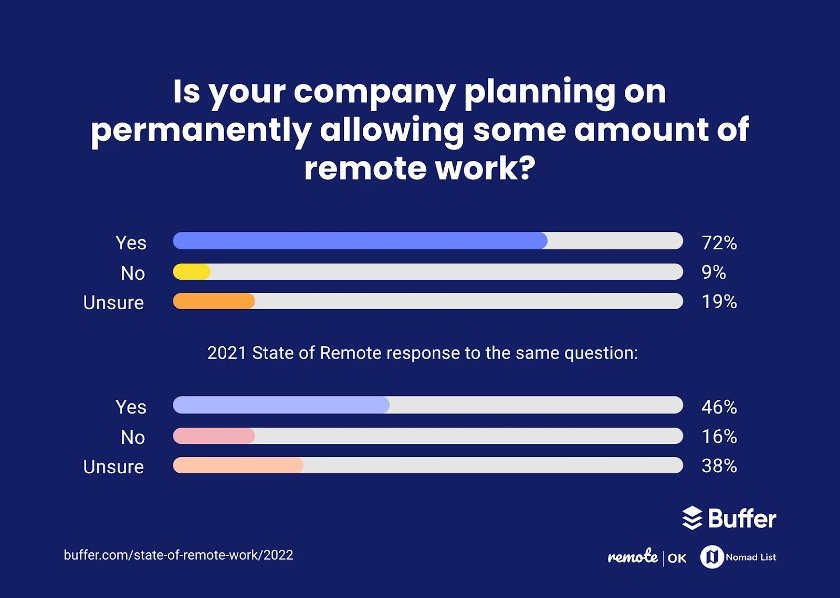
Business leaders and employers have realized the benefits of remote work, including reduced costs and improved efficiency.
But the growing adoption of hybrid and remote work policies introduces numerous security challenges for businesses. Malware attacks, phishing scams, data breaches – it’s a glimpse of threats that loom large over your organization.
Nearly 80% of business leaders say that their organizations are more vulnerable due to remote work.
The reason?
When your employees work on personal devices and unsecured networks, relying on traditional on-premise firewalls and VPNs isn’t enough. You need a more robust security protocol that protects devices, data, and applications irrespective of your employees’ locations.
That’s where the Zero Trust security model steps into the picture. In this blog, we’ll delve deeper into Zero Trust architecture and its best practices.
Let’s get started.
Decoding Zero Trust
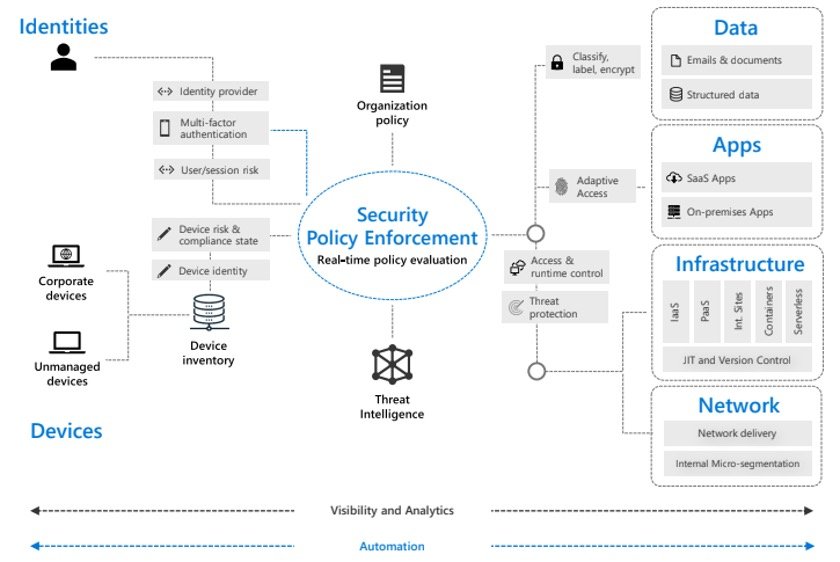
Zero Trust architecture is a security model based on the following principle – never trust, always verify. The Zero Trust model assumes breach and verifies every request before granting access. It treats every access request as though it’s originated from an unsecured network.
As a result, the Zero Trust model lets employees access confidential data and systems anywhere without compromising security. It involves authenticating a user’s identity, device, hosting environment, etc., and enforcing least privilege principles to prevent a breach.
Implementation of a Zero Trust model involves protecting the following foundational elements:
- Identities – People, services, or IoT devices that generate an access request
- Devices – On-site, partner-managed, or personal devices that are used to request access
- Applications – Legacy, cloud-based, or SaaS applications that a user wants to access
- Data – Confidential information about users, devices, applications, network, etc.
- Infrastructure – On-premise servers, virtual machines, micro-services, or containers
- Network – The infrastructure that connects different users and lets them access data
Zero Trust Best Practices
Deploying a Zero Trust security model involves several steps, including single-sign-on (SSO), multi-factor authentication, device/app management, micro-segmentation, and access control.
Here are a few best practices you can use to implement Zero Trust:
Extensive Verification
Start by authenticating and authorizing all available data points, including a user’s identity, device health, location, workload, and data classification. Single-sign-on and multi-factor authentication come in handy at this stage.
Enforcing Least Privilege Access
The Zero Trust model ensures data protection by limiting access using:
- Just-in-time privilege (JIT)
- Just-enough access (JEA)
- Risk-based adaptive policies
Assuming Breach
This step involves minimizing lateral movement using micro-segmentation. In other words, you have to segment access based on network, users, devices, and application. Also, you need to verify whether the data is classified, labeled, and end-to-end encrypted.
24/7 Monitoring
Monitoring systems and endpoints, and detecting attack vectors in real-time is a crucial step in the Zero Trust model. For this, you should build a dedicated incident response team that uses automated threat detection and alert management systems to monitor signals and tackle threats round the clock.
Zero Trust Implementation: Overcoming Roadblocks
Despite recognizing the importance of the Zero Trust model, many organizations struggle to deploy it. The possible reasons include a lack of expertise and operational support. Also, you’ll find it difficult to predict the costs involved in the process.
An easy way of overcoming these challenges is to find a company that offers Zero Trust as a Service. With Zero Trust as a Service, your security partner will monitor signals, analyze risks, and mitigate threats 24/7. Additionally, they’ll implement custom security and compliance policies based on your organization’s needs.
At ICT Solutions, we offer Zero Trust as a Service to handhold you through each step of implementing the model. We even provide a 1-hour service level agreement (SLA) for Tier 1 issues.
Get in touch with us today to reinforce your organization’s security framework.
